Greetings Humanoid, gorge yourself on information regarding the recently ancient art of Phreaking
Press with your 'mouse' the numbers on the Blue Box and dial in your request for knowledge.
Below for your comfort you find a directory of sorts
::::::::::::::::::::::::
| Numbah | :::::::::::: | Function |
|---|---|---|
| 1 | ---------> | What is it? (general information) |
| 2 | ---------> | Jobs and Wozniak |
| 3 | ---------> | Blue Box |
| 4 | ---------> | Cap'n Crunch |
| 5 | ---------> | VolPhreaking |
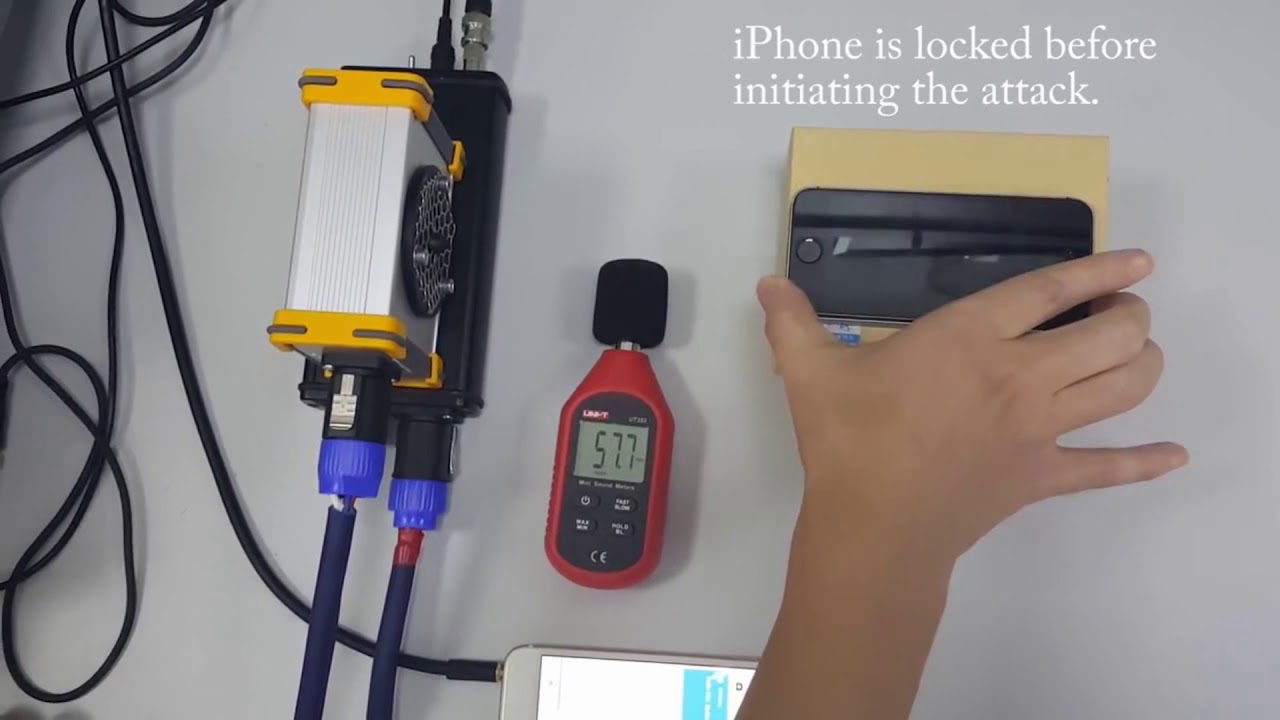
| 6 | ---------> | Video explaining the tech |
| 7 | ---------> | Old lecture on early Voice Over IP phreaking |
| 8 | ---------> | Video of Blue Box in action |
| 9 | ---------> | Phone Phreak Captain Crunch Rare Interview from '78 |
| 0 | ---------> | Site Credits |
Phreaking is a form of hacking that involves manipulating or exploring telephone systems, historically to make free or unauthorized long-distance calls. Emerging in the 1960s-70s, "phreakers" used specific tones, like 2600 Hz whistles or devices called "blue boxes," to trick automated phone networks. It is considered a precursor to modern cyber hacking.
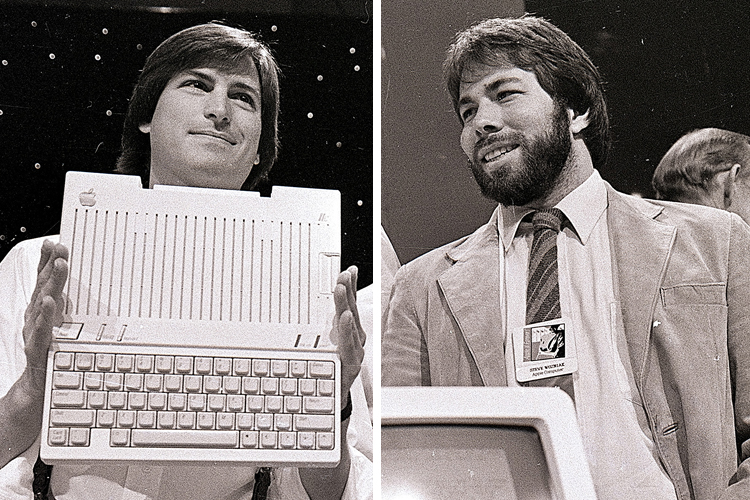
In the early 1970s, Steve Jobs and Steve Wozniak were involved in "phreaking," the act of manipulating telephone systems, by building and selling unauthorized "blue boxes". Wozniak designed a digital, highly advanced blue box that bypassed phone company charges, while Jobs handled the sales. They viewed it as a fun, educational challenge, with Wozniak noting that this experience was crucial to the creation of Apple.
A blue box is an electronic device that produces tones used to generate the in-band signaling tones formerly used within the North American long-distance telephone network to send line status and called number information over voice circuits. During that period, charges associated with long-distance calling were commonplace and could be significant, depending on the time, duration and destination of the call. A blue box device allowed for circumventing these charges by enabling an illicit user, referred to as a "phreaker", to place long-distance calls, without using the network's user facilities, that would be billed to another number or dismissed entirely by the telecom company's billing system as an incomplete call.

In the late 1960s and early 1970s, a toy "Bo'sun whistle" found in Cap'n Crunch cereal boxes became a legendary tool for phone phreaking, a predecessor to modern hacking. The whistle happened to emit a nearly perfect 2600 Hz tone, which was the exact frequency ATandT used to signal that a trunk line was idle and ready for a new call.
VoIP phreaking is a form of cyberattack where hackers exploit vulnerabilities in Voice over Internet Protocol (VoIP) systems to commit fraud, such as making unauthorized long-distance calls, accessing voicemail, and stealing billing information. It is often used for toll fraud, costing businesses significant money.
__/\\\\____________/\\\\_____/\\\\\\\\\_____/\\\\\_____/\\\__/\\\\\\\\\\\\\\\_
_\/\\\\\\________/\\\\\\___/\\\\\\\\\\\\\__\/\\\\\\___\/\\\_\/\\\///////////__
_\/\\\//\\\____/\\\//\\\__/\\\/////////\\\_\/\\\/\\\__\/\\\_\/\\\_____________
_\/\\\\///\\\/\\\/_\/\\\_\/\\\_______\/\\\_\/\\\//\\\_\/\\\_\/\\\\\\\\\\\_____
_\/\\\__\///\\\/___\/\\\_\/\\\\\\\\\\\\\\\_\/\\\\//\\\\/\\\_\/\\\///////______
_\/\\\____\///_____\/\\\_\/\\\/////////\\\_\/\\\_\//\\\/\\\_\/\\\_____________
_\/\\\_____________\/\\\_\/\\\_______\/\\\_\/\\\__\//\\\\\\_\/\\\_____________
_\/\\\_____________\/\\\_\/\\\_______\/\\\_\/\\\___\//\\\\\_\/\\\\\\\\\\\\\\\_
_\///______________\///__\///________\///__\///_____\/////__\///////////////__
____/\\\\\\\\\_________/\\\\\\\_______/\\\\\\\\\________________/\\\\\_
__/\\\///////\\\_____/\\\/////\\\___/\\\///////\\\__________/\\\\////__
_\///______\//\\\___/\\\____\//\\\_\///______\//\\\______/\\\///_______
___________/\\\/___\/\\\_____\/\\\___________/\\\/_____/\\\\\\\\\\\____
________/\\\//_____\/\\\_____\/\\\________/\\\//______/\\\\///////\\\__
_____/\\\//________\/\\\_____\/\\\_____/\\\//________\/\\\______\//\\\_
___/\\\/___________\//\\\____/\\\____/\\\/___________\//\\\______/\\\__
__/\\\\\\\\\\\\\\\__\///\\\\\\\/____/\\\\\\\\\\\\\\\__\///\\\\\\\\\/___
_\///////////////_____\///////_____\///////////////_____\/////////_____